4 Mar 2026 | A Year In OT Security
Congratulations. You’ve completed the OT Security Weekly Plan. If you are like most people, some weeks were a lot more helpful than others. Some weeks easier than others. There might have even been some weeks where you said, Dale is just wrong about this. All this is...
9 Feb 2026 | A Year In OT Security
The last day of S4 we open up Stage 2 for one hour of 5-minute Unsolicited Response talks. Any attendee can come on stage and present for 5 minutes (but not a second more than 5 minutes). Some are research results or questions; others are big ideas, problems that need...
2 Feb 2026 | A Year In OT Security
If you take one thing from this book, my hope is it leads you to focus on OT cyber risk management rather than slavishly trying to implement and maintain a long list of good practice OT security controls (cyber hygiene). SANS and many others, including me, have put...
26 Jan 2026 | A Year In OT Security
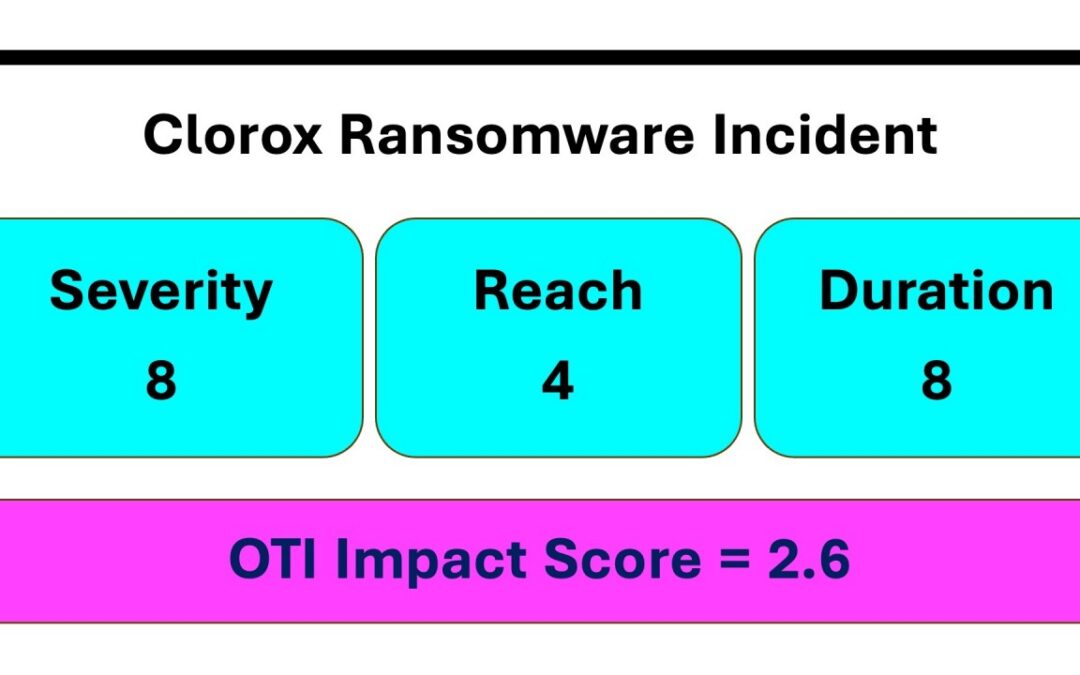
Warning: This is the most difficult task in this book for most people. OT cyber incidents and their consequences are lagging indicators. The bad event that caused the impact has already happened. While it is important to capture and present the information you...
19 Jan 2026 | A Year In OT Security
You identified three to five of your company’s key mission metrics in Week 10 of last year. This week consider if any OT security incidents affected these key mission metrics in 2025. If possible, determine the percentage impact of the OT security incidents to all...