Europe, Regulation and AI with Patrick Miller
Click To Subscribe Show Notes Patrick Miller has OT cybersecurity experience as an asset owner, PacificCorp. As a regulator and one of the first NERC CIP auditors with WECC. As a community organizer creating and leading EnergySec and the BeerISAC. And as an...
Tom Alrich Book Interview: Introduction To SBOM And VEX
Click To Subscribe Show Notes Tom Alrich is the author of the new book Introduction To SBOM And VEX. Host Dale Peterson and Tom discuss: Who Tom wrote the book for. Why the book had so much content prefaced by “in the author’s opinion” and “the author believes”. Early...
US National Cybersecurity Strategy Implementation Plan V2.0
This is the first iteration of the Implementation Plan, which is a living document that will be updated annually. US National Cybersecurity Strategy Implementation Plan, July 2023 We should be seeing the annual update, Version 2.0, of the Implementation Plan this...
A Barbell Strategy For OT Security
The barbell strategy is most common in finance and became more widely known after its use in Taleb’s Antifragile. Barbell Strategy: A dual strategy, a combination of two extremes, one safe and one speculative, deemed more robust than a “monomodal” strategy;...
Clorox Investor Cyber Incident Concerns
Lost Manufacturing Capacity & Recovering Shelf Space Clorox had suffered a cyber incident on their enterprise network, not OT, in August of 2023. They lost 26% of their manufacturing capacity during that quarter as they had to move to manual order processing....
Water Hysteria and Reality
Reality There has not been a publicly disclosed cyber incident on a US water utility’s OT system that has affected the delivery of safe, drinkable water for years. There has not been a publicly disclosed cyber incident that can even be called a near miss. Not...
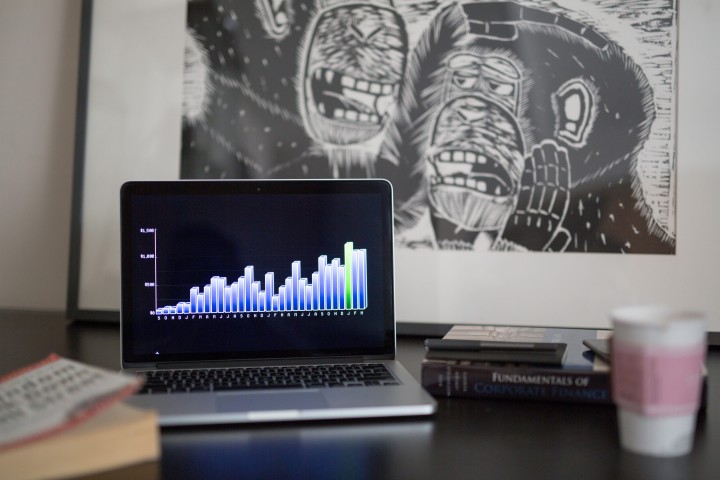
Tough Times In The OT Security Job Market
There was one sour note amongst the good feelings as the S4 community met in early March – – some were missing because they had been laid off. Talented, innovative professionals who had their choice of jobs not too long ago. The OT security job...
The Security Floor … Not Secure By Design
It hit me during Megan Samford’s bullish comments on Secure By Design at the S4x24 Closing Panel. She believed it was possible to specify a minimum set of required security configuration parameters, development processes and security controls. While Megan referred to...
