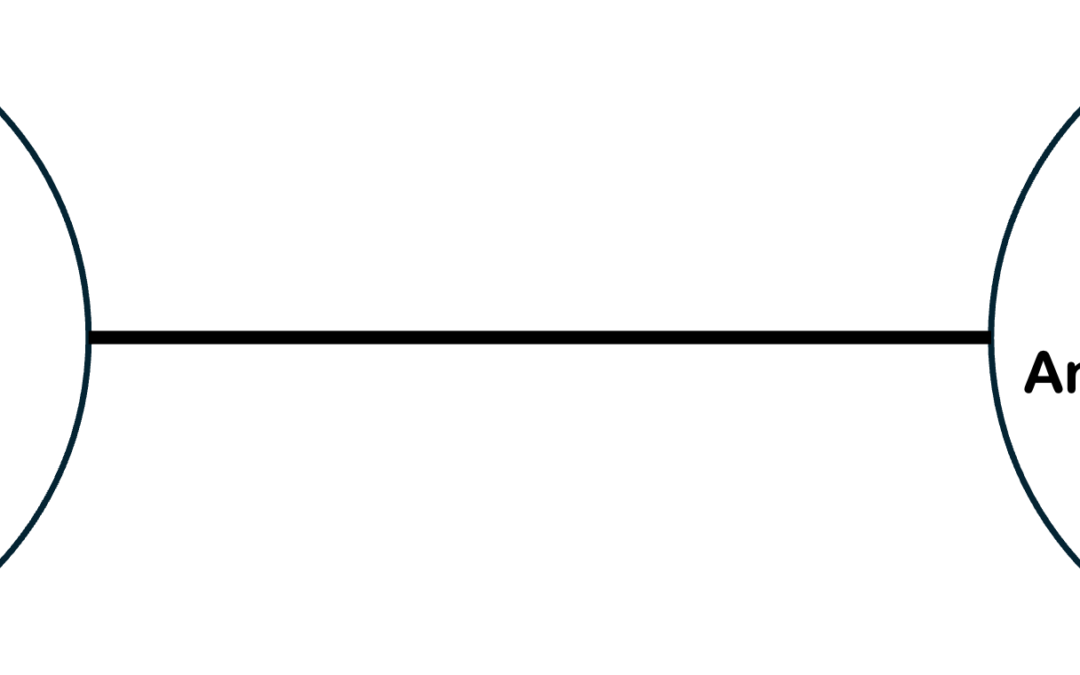
The barbell strategy is most common in finance and became more widely known after its use in Taleb’s Antifragile.
Barbell Strategy: A dual strategy, a combination of two extremes, one safe and one speculative, deemed more robust than a “monomodal” strategy; often a necessary condition for antifragility.
The barbell approach could be used on anything where the actions or results fall on a spectrum, including OT security. It is essentially what I recommended for small water utilities in my article two weeks ago.
Asset owner executives, government officials, and occasionally cybersecurity vendors will talk about the millions of time each day they are attacked. An ‘attack’ could be something as simple as the Internet firewalls blocking reconnaissance, a spray and pray attempt, or even an unauthorized, but non-malicious communication attempt. A small number of simple, inexpensive controls can stop 99.999% of these attacks.
On the other end of this spectrum are the nation-state or other highly talented and resourced threat actors who are after a specific objective on a specific target and willing to spend time to achieve their objective. These are a tiny percentage of all attack attempts, and they are the attacks that are hardest to stop – – even with a mature security program. Applying many additional expensive security controls may not stop them.
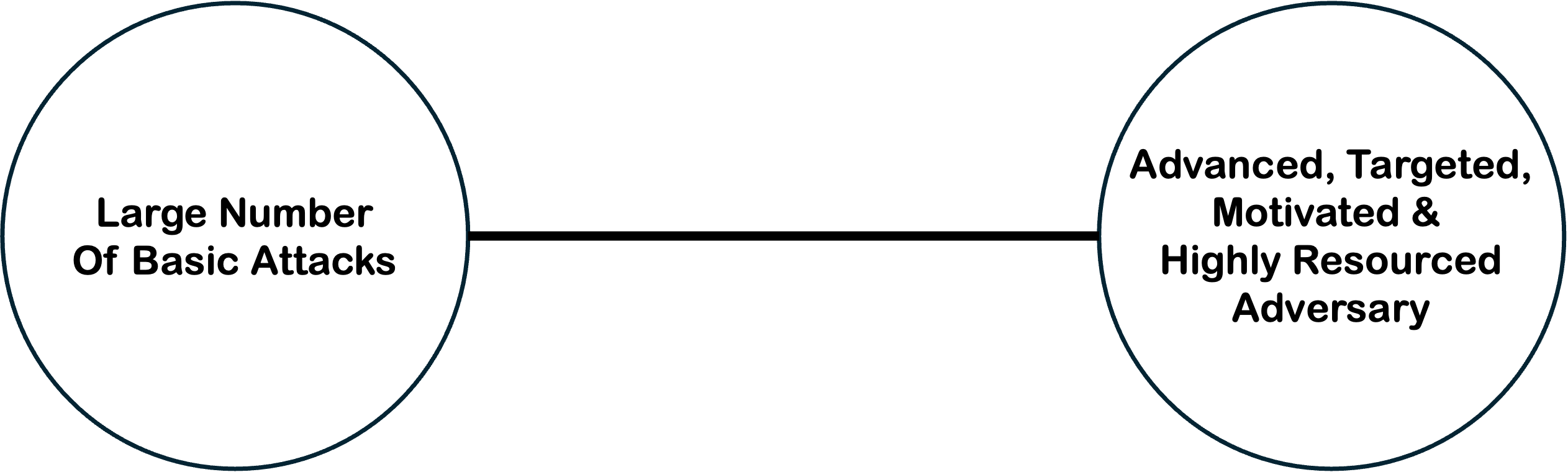
This barbell look at the threat can lead to a barbell approach to spending resources to manage the related risk.
Asset owners should attack each end of the threat / threat actor barbell. What do you need to do to stop the large number of basic attacks from affecting OT, the 99.999%? I suggested for small water utilities, and likely most others, it could be as simple as:
- No direct Internet access to OT
- An OT security perimeter (even a router ACL so no equipment cost)
- Dedicated USB drives for OT
- Two-factor authentication if remote access is required
The other end of the barbell is recovery. Recovery of the ability to deliver the product or service to your customers if the cyber attack succeeds. This may or may not require recovery of OT or IT cyber assets,
Forgo the items in the middle of the spectrum until you are confident in the weights on the ends. Additional security controls likely will protect or detect some of the additional .001% of the attacks, but not all of them.
Nuance Notes
- Preventing other high consequence events should be added to the Recovery side of the barbell. For example, preventing damage to expensive equipment with unhackable protection measures or preventing a cyber attack that succeeded from causing an unacceptable safety or environmental condition. Recovery primarily addresses the customer impact and part of the financial impact portions of risk.
- As your program matures, increase the size of the weight on each side rather than focus solely on the more security controls to reduce likelihood,
- This approach is at odds with most government and industry efforts to document a long and growing list of security controls necessary to meet cyber hygiene. You may be required to implement a set of security controls to address regulatory risk. You should document the risk reduction achieved via your approach as opposed to a standard or guidance documents recommended security controls.