29 Oct 2019 | 2019, Strategy
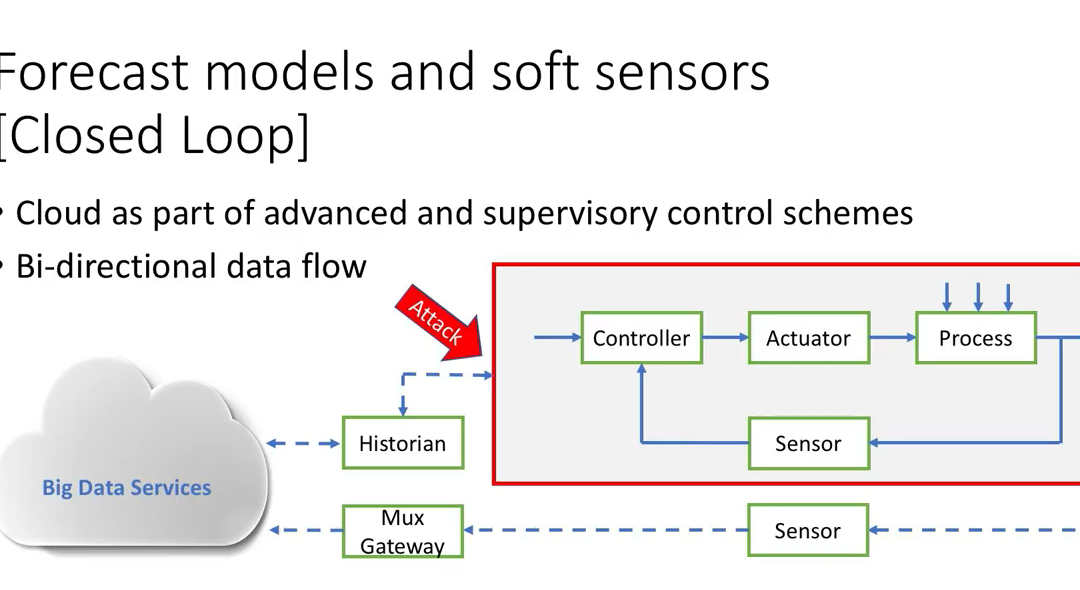
Most of the activity in the ICS security product market has been around passive solutions that create asset inventories and detect cyber incidents. It is a bit astounding that the market and solutions will look almost completely different in two to five years than...

29 Oct 2019 | 2019, Podcast
http://traffic.libsyn.com/unsolicitedresponse/2019-14_Marina_Krotofil.mp3 Marina Krotofil has been able to view the ICS security world from a number of perspectives. Beginning as an academic; working for an ICS vendor (Honeywell); working for an ICS security products...
17 Oct 2019 | 2019, Podcast
http://traffic.libsyn.com/unsolicitedresponse/2019-13_Sean_McBride.mp3 In this episode Dale interviews Sean McBride. Sean was on some of the earliest Unsolicited Response episodes when he was a Founder and Analyst with Critical Intelligence, the first ICS Threat Intel...
6 Oct 2019 | 2019, Podcast
http://traffic.libsyn.com/unsolicitedresponse/2019-12_Miller.mp3 I took the opportunity to interview Patrick Miller while we were both in Sochi speaking at the Kaspersky KICS event. Patrick is a Founder and Managing Partner of Archer International, and he has been a...
14 Aug 2019 | 2019, Podcast
http://traffic.libsyn.com/unsolicitedresponse/2019-11_Closing_Panel.mp3 The S4 Closing Panel is always a candid discussion on where the community is in securing ICS, where we are succeeding and where need to do better. This year I was joined by Rob Lee of Dragos and...