Different Approaches To EU’s NIS2 Has An Upside
The Tenth Amendment to the US Constitution states: The powers not delegated to the United States by the Constitution, nor prohibited by it to the States, are reserved to the States respectively, or to the people. The states are often referred to as "laboratories of...

Needed: Outrage Management
Peter Sandman introduced the following risk equation in the 1980's: Risk = Hazard + Outrage An increasingly common scenario in the OT world the last two years, particularly with small scale water incidents, is Hazard is Low and Outrage is High. In these cases the task...
Mandating Cyber Incident Disclosure
SEC and CIRCIA Different Aims, Different Progress, Different Results SEC The US Security and Exchange Commission (SEC) proposed draft rules to disclose cyber incidents with a material impact in March of 2022. The rule was finalized and went into effect in December...

Checklist v. Risk Based OT Cybersecurity Regulation
Why Checklists Win Talk to most security professionals, OT and IT, and they'll tell you that applying a checklist approach to security controls across an industry sector makes no sense. Compliance to a standard or regulation does not equal security. Each company...
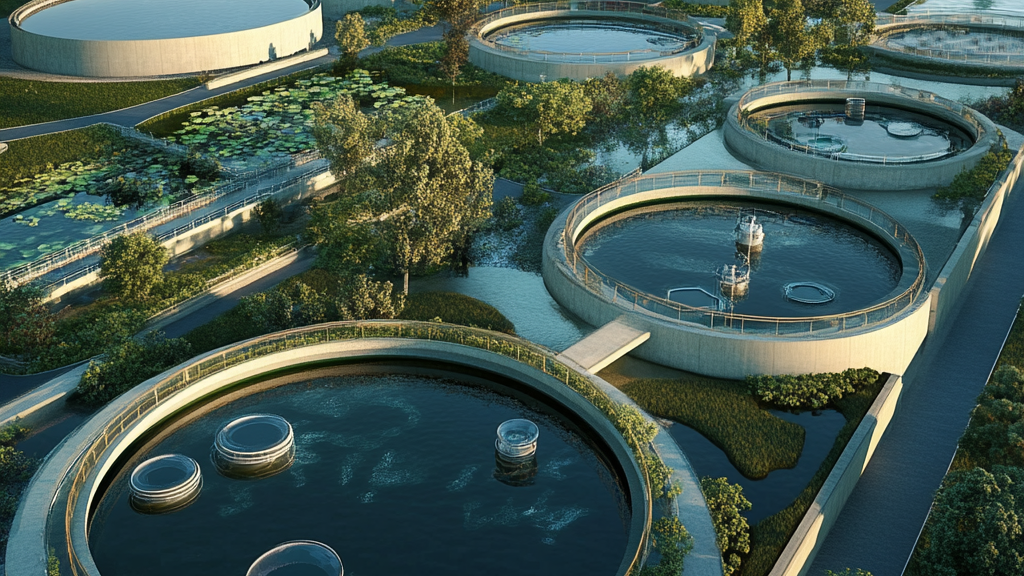
OT Security Is A Great Career
I was hooked on OT Security from day one. During my first SCADA security assessment in 2000 we went out to see damns, pumping stations, turnouts and other physical systems along a canal. This was much more interesting than sitting in a conference room or a data...

Questions on AI in OT & ICS Security
Unsurprisingly the largest category of submissions to S4x25 CFP have been AI related. Almost all of these submissions could have been written by generative AI. A paragraph or three on how AI is an important, fast growing technology that will have a major impact on OT...

How Successful Is Your Standard?
Thomas Burke, longtime President of the OPC Foundation, had the best answer to this question in a podcast interview with Walker Reynolds. Success is measured by the level of adoption. That's the key, when you go do anything with industry standards they've got to be...

Embedded PLC Security Is Happening
From 2001, the advent of ICS security, until 2019 PLC security was a "bump-in-the-line". Place a Tofino or other industrial security solution in the network path to secure network communication to and from the PLC. This was widely understood to be a sub-optimal and...

How Would You Like Your OT Remote Access?
You can always count on Waterfall to take a different approach to solving a security need. (this is a good thing). They recently announced their Hardware Enforced Remote Access (HERA). HERA leverages Waterfall’s unidirectional technology (one-way, hardware enforced,...

FrostyGoop: 2004 Is Calling
And Still Awaiting Calls To Replace Unauthenticated Protocols Today Dragos released information on ICS malware they are calling FrostyGoop. The key lines from the release are: "It is the first ICS-specific malware that uses Modbus communications to achieve an impact...
GET DALE'S ICS SECURITY NEWS & NOTES EMAIL EVERY FRIDAY
Article Archive By Year
Article Archive By Category
UPCOMING EVENTS
S4x24 ... 4 - 7 March 2024 in Miami South Beach
Save the date. For the biggest and most future focused on ICS Security Event.
