
The OT Cyber Incident And Threat Dichotomy
The impact of OT cyber incidents, excluding ransomware on IT, has been less than 1% of all cause OT outages and OT related financial loss. A motivated and skilled OT cyber attacker could cause a high or catastrophic incident on many OT systems in almost every sector....
Reducing OT Incident Impact Inflation
Where does the media get the information and quotes that turn a couple of residential swimming pools of water spilling out of a water tank (Muleshoe) into a major story and congressional hearing ... from us, the OT security community. Since we are part of the problem,...

S4x26 Theme Keynote: Connect
Below is what I intended to say on stage. It always varies a little bit live. The video will be out next week. Each S4 Conference has a single word theme. This year's theme is Connect. Connections are exciting, unpredictable, scary, they bring opportunity, and for...
First Nozomi, Now Armis
2025 saw two of the four top tier OT detection + asset inventory vendors get acquired. First Mitsubishi Electronics acquired Nozomi Networks at a valuation of $950M (read my analysis of the Nozomi acquisition). Then last month ServiceNow announced they will be...

25 Years, 3 Lessons
I'm finishing my 25th year focused on OT security (called SCADA security when I started, then ICS security, and now OT security). So many failures, successes, changed analysis, and lessons learned over that time. Here are 3 lessons that I wish hadn't taken me so long...

Premature Consensus In OT Security Made Worse With AI
We know very little about what security controls and consequence reduction actions reduce the number and impact of incidents that includes an OT cyber component. Read that again. We have hypotheses. I have hypotheses, and wrote a book on the topic A Year In OT...
Two OT Security Debates
We've had some great debates on the S4 stage. One of my favorites was a debate I had with Eric Byres entitled Is Eric Byres a SCADA Apologist or a SCADA Realist?. The key to a good debate is to find an issue where a 10% - 25% minority of the audience has a strong...
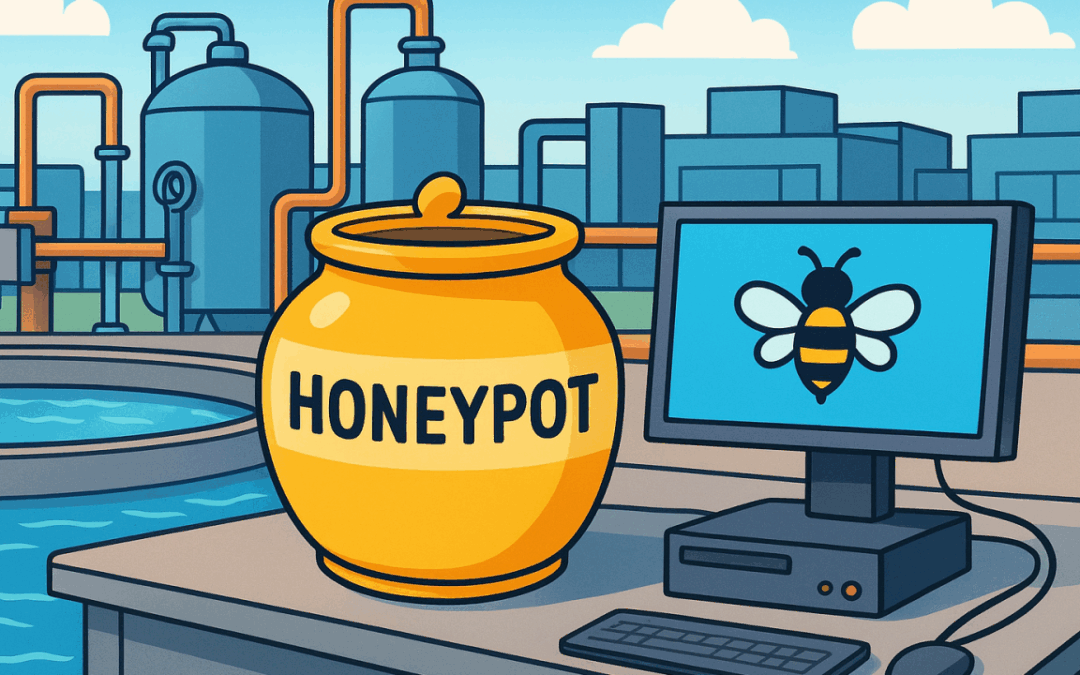
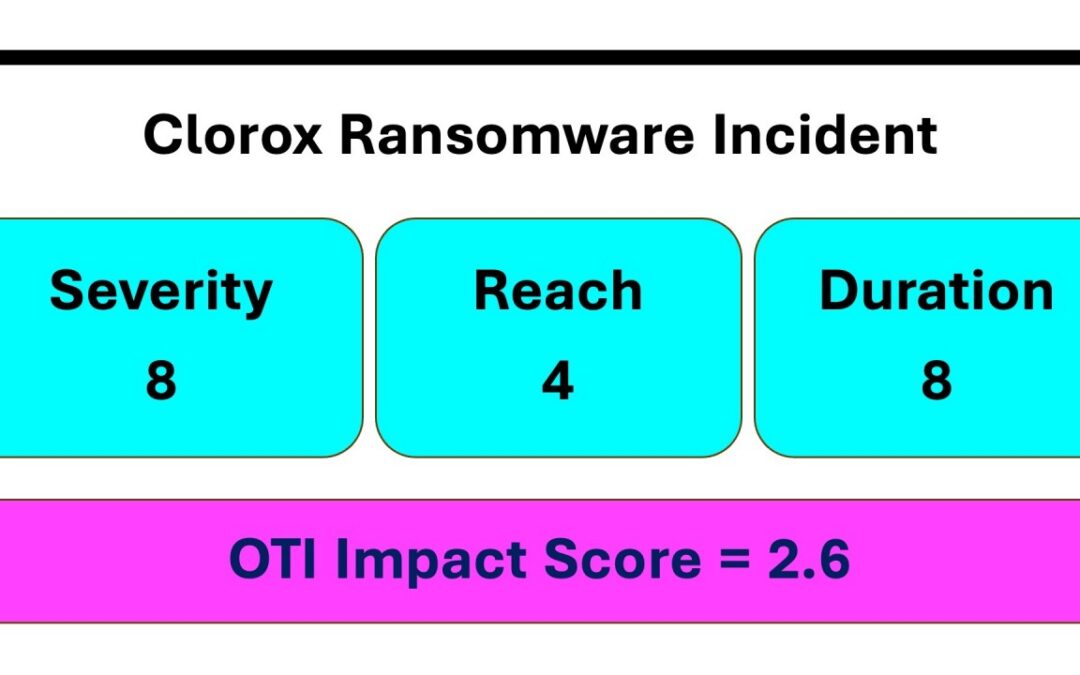
Water Treatment Honeynet Incident Analysis
Forescout's Verdere Labs reported that a honeynet posing as a water treatment system was compromised by TwoNet, a Russian-aligned group. According to the blog entry TwoNet caused: Defacement: Login page changed to HACKED BY BARLATI, F*** Process Disruption: Deleted...

OT Is The Venice Of Security Infrastructure
I get tired of writing that 90%+ of the OT protocols used to communicate with PLC's and other Level 1 devices (and Level 0 ... hello Joe) are insecure by design. They lack cryptographic authentication of the source or contents, intentionally. They were designed to...

What Is The True Level Of OT Cyber Incidents?
This article attempts to frame the question after my back and forth with Robert M. Lee last Friday. Question: How many cyber attacks are resulting in non-trivial consequence events in OT / Operations? Stipulation 1: Ransomware and other causes of outages on IT cyber...
GET DALE'S ICS SECURITY NEWS & NOTES EMAIL EVERY FRIDAY
Article Archive By Year
Article Archive By Category
UPCOMING EVENTS
ENTELEC ... 7 April 2026 in Galveston, TX
I'll be giving the keynote: Connect, Consider, and Consequence at this event for the oil & gas sector.
S4x27 ... 8 - 11 February 2027 in Tampa
Save the date for S4x27. For the biggest and most future focused on ICS Security Event ... and now in our new and larger venue in Tampa.
